I don't know how many CFan's buddies had passed the Children's Day. When Xiao Bian asked for vacation, the editor-in-chief was very happy to approve and issued the following figure to approve Xiao Bian's application.
“Fire and anti-theft anti-bear child†is the golden rule that guarantees computer security. Well, now one more thing needs to be added: Prevention of Software Family Barrels. We do not look at Xiaobian to do this test every day, share that software, can make the computer on the hand not die blue, relying on the habit of years to develop, always Shadow Defender (shadow guard) as one of the startup project.
Simply put, Shadow Defender is able to protect the Windows system and restore tools under certain conditions. It is a shadow system that has been popular for a while. PowerShadow is similar to its function. We choose to pick ourselves up based on our preferences.
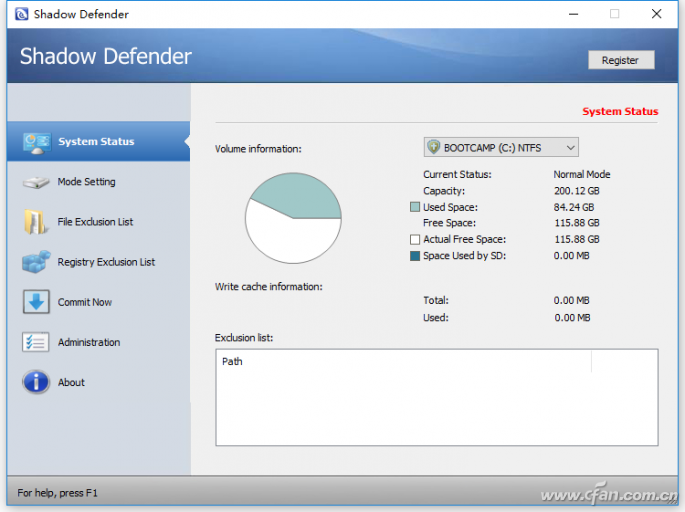
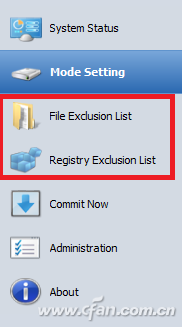
After starting, enter "Mode Setting" and click "Enter Shadow Mode" to enter the selected disk partition into "shadow" mode.
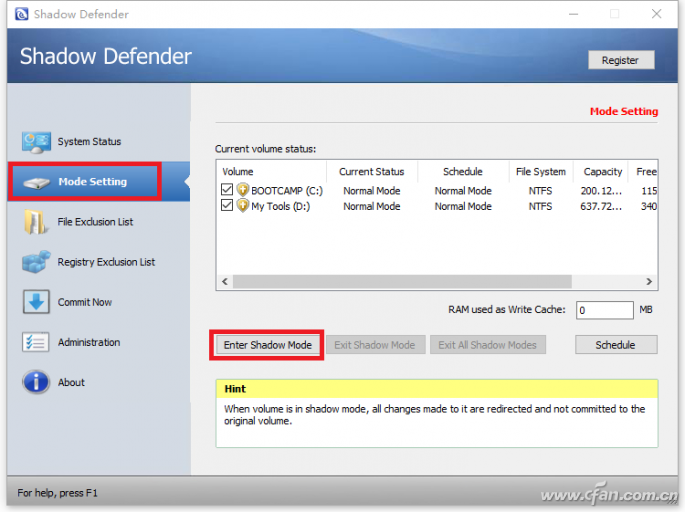
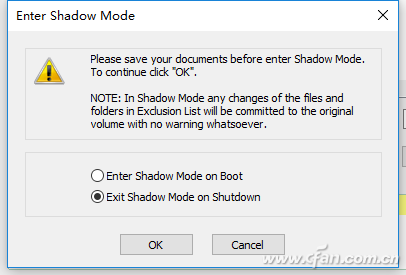
The partition under “shadow†protection will restore the previous system operation and software installation according to your settings. “Enter Shadow Mode on Boot†will continue to protect the system after reboot, and will not record any changes to the partition. Set, and "Exit Shadow Mode on Shutdown" will exit the shadow mode after the shutdown, which means that the protection state is invalid, and any subsequent operations will affect Windows. If you are ready to do something dangerous, you must check this setting.
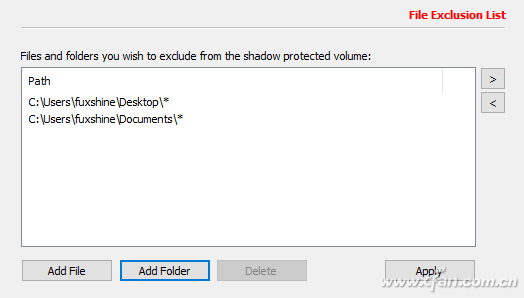
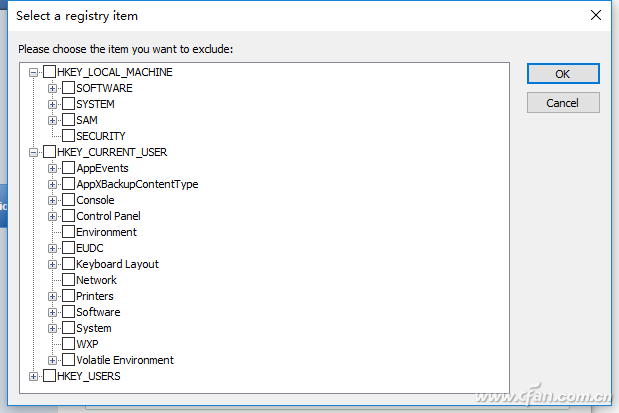
Oh, you ask Xiao Bian how to test the edge code words, to ensure that the system under the safe revertible protective measures, but also to retain some of the places that can be changed? Did you see the two options on the left side of the software interface?
The former can add files or folders to the shadow mode exclusion list.
The latter can cancel the protection of some branches under the registry, so Xiaobian not only can see the effect of the system modification at any time when doing some tests, but also can promptly record and restore it to the state before the test.
These can not only help you test whether some software has a "home-bucket" package, and it is also very effective to deal with bear children who play computer games.
It should be noted that the Shadow Mode can handle so much. It is impossible to expect it to reject viruses and Trojan horses. Some malicious programs will not damage the system but will steal personal data. With penetrating ability, it will directly make the computer into this.

Therefore, in the normal use of security software, the use of shadow mode is only a protection measure for setting and changing the system. Do not think that it is a panacea (ugly words must be said in front, otherwise the problem Xiaobian can back Can't afford that pot).
Neodymium Tweeter,Tweeter Horn Driver,Neodymium Compression Driver,Neodymium Speaker Drivers
Guangzhou Yuehang Audio Technology Co., Ltd , https://www.yhspeakers.com