In the era of economic and technological development, big data and the Internet continue to infiltrate in different fields and penetrate into all walks of life, which not only provides basic guarantee for its own expansion, but also facilitates the development of various industries. The security alarm industry has also undergone tremendous changes under the influence of big data. Most alarm service providers have become more and more aware of the impact of the external industry downturn on their business operations and the national “Internet +†and “Big Dataâ€. "The promotion of the.
Big data balances user and vendor needsThe security alarm industry is a special industry based on results appeal and orientation. For the customer, its core concern is security. The result is that the benefits are not lost. In a sense, it is a kind of sensibility. Sensitive indicators that are difficult to quantify. For the service provider or equipment manufacturer, its core concern is the alarm, and the result is the accuracy and timeliness of the alarm. These are rational expressions that have objective technical parameters and metrics, and big data can effectively balance these two needs.
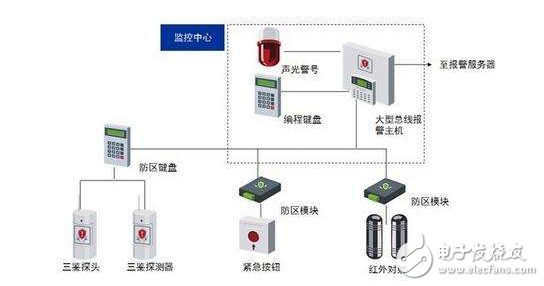
Users: By analyzing big data, we can analyze the false alarm rate of each device, the frequency of equipment failure, etc., so as to select the inexpensive equipment to provide users, and systematically optimize and improve the function of the security alarm system. performance. The alarm process is actually a test field for testing the functional design and performance indicators of the alarm system. The working process of the alarm system involves front-end detection, host control transmission, central machine (server) reception processing, and platform software compilation and conversion. The identification and utilization of many of the data has lost the meaning of system networking.
The application of alarm services to big data is actually related to the daily use needs of users and the provision, optimization and improvement of security alarm services. On the one hand, it has a directional guidance for unified standard formulation and personalized satisfaction for different customer groups, different installation and use locations, different system activation periods, different security service claims, and other personalized service content; On the other hand, it is convenient for operators to launch more types of service content according to market and user feedback. At the same time, it can mine and guide more forms of security alarm service according to the trend of some requirements, and then open up new alarms. Service market. For example, the traditional anti-theft alarm is extended to the security alarm, and the fixed point alarm is extended to the mobile target alarm.
Service provider or equipment manufacturer: Through big data, the cause of the alarm can be analyzed. For example, when the air is dry in autumn and winter, the situation of fire will be greatly improved, then the relevant measures can be done in advance, and the departments are notified in advance. Coordination; by analyzing the specific time period, for example, there will be frequent accidents during the holiday season, then the next time the festival can be related to the relevant arrangements; through the flow statistics, statistics on the visits of a certain area, to the business Provide a reference.
During the operation of the alarm system, we can organize and analyze a variety of useful information that is more in line with the actual application and carry out targeted optimization and improvement. For example, the sensitivity adjustment problem of the temperature sensor, the working life problem of the humidity sensor, the contact force of the pressure sensor in the face of the detection accuracy and accuracy, the stability of the host control system and the speed and accuracy of the data transmission, the central machine Or the problem of the response rate of the server to the reception, storage and processing of the alarm data, the conversion and compilation of the various data information by the platform software, and the like. This series of optimization and improvement of technical parameters requires a large amount of daily alarm process data accumulation and analysis, and a specific performance indicator is adjusted to meet different usage scenarios, different use objects, and different Use time period for personalization of security and convenience. Analyze the number of alarms in each area for a period of time, so that you can focus on the allocation of related resources.
Future alarm service will be fast, accurate and accurateAs electronic information technology becomes more and more developed, especially when big data collection and application is getting hotter and hotter, there is no technical difficulty in carrying out basic or even comprehensive data collection, but the collection, collation, analysis and utilization of data is The real "big data" connotation, especially in the security alarm industry - from this perspective, most of the current alarm service companies, despite the name of "big data applications", are actually far from the application. .
The future alarm is not only a simple interaction process between the alarm center, the police personnel and the user, but a comprehensive alarm body based on the Internet, handheld devices, etc., which integrates various software and hardware. The alarm center monitors the scene in real time through video surveillance. When the alarm is triggered, the alarm center can quickly determine which type of alarm is currently connected to the live video for review. When it is confirmed that the police needs to be alerted after the review, the center will locate the nearest police officer from the alarm point by GPS, and forward the alarm information and the live video image to the APP software of the police personnel, and provide optimal navigation through the electronic map navigation function. The route is convenient for police officers to arrive at the scene in the first time. After the police officers arrive at the scene, they can take photos and videos through the handheld device, and transmit the live data back to the center for analysis and preservation in real time.
In actual use, for some VIP users, such as banks, gold stores, coal mines and other high security scenarios, the method of checking out the alarm can be used. When the VIP user receives the alarm, the alarm center automatically forwards the alarm information to the alarm in the domain. Personnel, and the current video is directly transmitted to the police officers. In the process of rushing to the scene, the police officers cooperate with the center to review the situation on the spot and truly realize the mobile connection police.
Nowadays, more and more security alarm service customers have begun to put forward many requirements based on big data applications for daily services. At the same time, many operators who are exploring the outward development of the security alarm industry have already had relatively clear ideas and directions. After all, relying on price competition to seize the market is by no means a long-term solution. The low price can only provide users with worse service. In the future, the security service market will be further liberalized. More and more enterprises and people of insight will enter this field and will give the whole The market has a greater impact, eliminating companies that are small, poorly serviced, and have less service.
Nowadays, manufacturers and service providers have begun to adopt new ways of piloting cooperation. While further strengthening their data processing capabilities, they filter the severity of the alert to match the corresponding processing plan. Through the application of the platform data processing technology, different devices are connected to the service system, so that the police information can be grasped in time and at any time, and the frequency of false alarms is minimized. More efficient sharing advantages, give users a satisfactory answer, thereby improving user stickiness, reasonable avoidance of user satisfaction and user churn. Enterprises that pursue the company's operations and industry development should show such eyes and minds in a timely manner, so that the security alarm industry can renew its vitality under the impact of the full-scale market economy.
Conclusion: The times have been changing, and the development of technology is changing with each passing day, but the demand for security is consistent, and the alarm industry that meets security needs will continue to play an important role for a long time. In the era of technological innovation and service innovation, security enterprises should improve their core competitiveness by absorbing talents, technological innovation, and improving the technological content of products, and accelerate the transformation to technology-based enterprises. At the same time, they should seek opportunities to seize opportunities in diversified market segments. Market, create customized professional routes, tailor solutions to meet the needs of industry users, and retain customers with good service. I believe that as long as we continue to deepen the industry and understand consumers' demands in a deeper way, we will not stick to the traditional alarm industry thinking, and the development prospects of the industry are still good.
All In One Business Computer is the one of the important All In One PC series, can meet all enter and normal business application scenarios. Therefore, more and more clients choose and recommend this Business All In One Computer for business or education projects. The Best All In One Computer For Business is the similar Apple design, competitive and attractive, the hottest parameters is 19 or 21.5 inch intel i3 or i5 2th or 3th or 4th 4 gb ram 128GB ssd . There are many other all In One Computers For Business with lighter weight. Of course, you can see Colorful All In One Gaming PC, All In One Desktop Touch Screen and All In One Business Pc. Believe you can always find the right one at this store. To save time, You can also contact us by email or calling directly to get matched and valuable information fast.
Any other special configuration interest, also feel free to let us know, will try our best to back you up.
Except all in one Custom All In One PC, 14 inch Education Laptop and 15.6 inch business laptop also available here.
All In One Business Computer,Business All In One Computer,Best All In One Computer For Business,all In One Computers For Business,All In One Business Pc
Henan Shuyi Electronics Co., Ltd. , https://www.shuyiaiopc.com